Empowering Your Defense Strategy
Our seasoned practitioners bring a wealth of experience, ensuring that our cybersecurity solutions are not only aligned with industry standards but also tailored to meet the unique challenges of our clients.
Lumifi leverages proprietary technology to stay at the forefront of cybersecurity innovation. Our cutting-edge tools and solutions are designed to provide clients with a competitive edge in the ever-evolving threat landscape.
Recognizing that every organization is unique, Lumifi offers tailored security services that address specific needs and challenges. This customization ensures that our clients receive the most effective and efficient cybersecurity solutions.
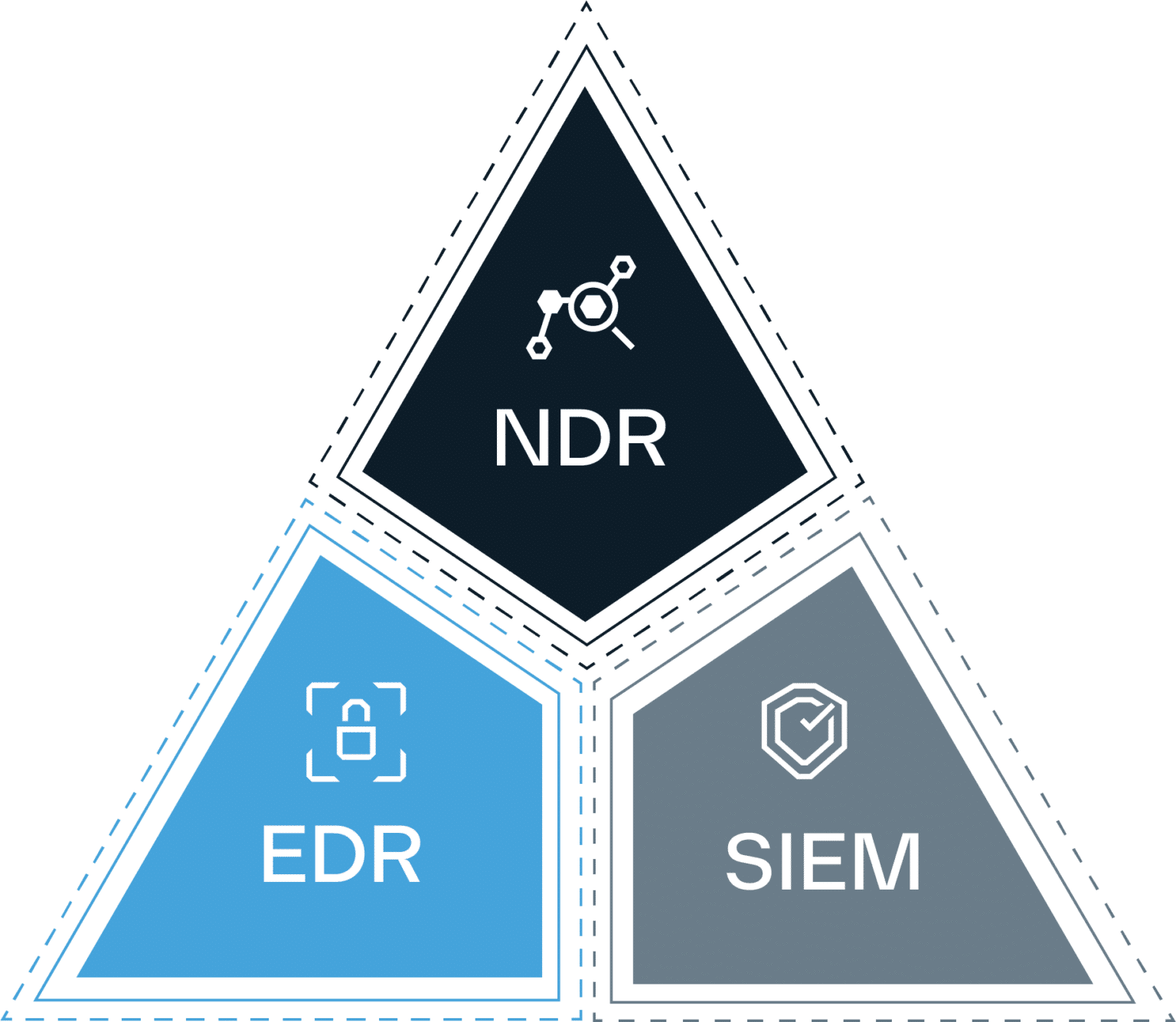
Simplify Security Log Management with ShieldVision™ SLM. Take the first step towards the SOC Visibility Triad. Make sense of high-volume security logs with Lumifi.